Booking.com Got Breached. Your Front Desk Is the Actual Attack Surface.
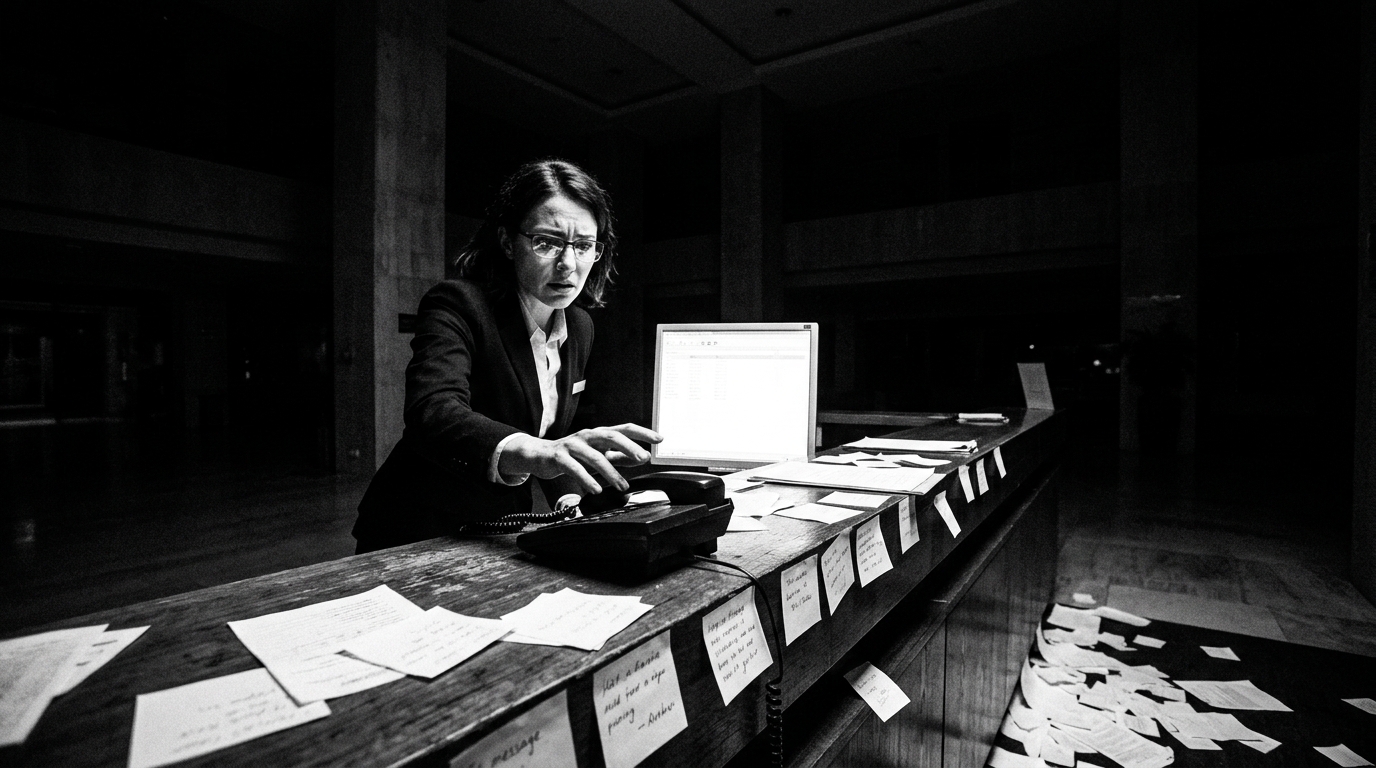
Criminals aren't hacking Booking.com's servers directly... they're phishing your hotel staff, stealing booking data, and then scamming your guests with messages that look exactly like they came from your property. The breach notification went out April 13, but the real question is what your night auditor would do if they got a suspicious link at 2 AM.
So here's what actually happened. Booking.com started notifying customers on April 13 that someone got unauthorized access to booking data... names, emails, phone numbers, addresses, reservation details, property names, travel dates. Everything except (they claim) financial information. The attack vector? It wasn't some sophisticated zero-day exploit against Booking.com's infrastructure. It was phishing. Specifically, a technique called "ClickFix" that tricks hotel employees... your employees... into installing malware on property-level systems. The criminals compromise the hotel's Booking.com extranet access, harvest the reservation data, and then impersonate the hotel to scam guests into fake payments. Booking.com's own CISO flagged a 500-900% increase in AI-driven travel scams over the prior 18 months. That was back in June 2024. Two years later, here we are.
Let me be blunt about what this means. The hotel is the entry point. Not Booking.com's servers. Not some shadowy hacker collective targeting cloud infrastructure. Your front desk agent. Your reservations manager. The person who opens an email that looks like it came from Booking.com support asking them to "verify their account" or "update their login." I consulted with a hotel group last year that had three properties compromised through almost exactly this method... a staff member clicked a link in what looked like a routine extranet notification, malware installed silently, and within 48 hours the criminals had every active reservation in the system. The GM didn't find out until a guest called to ask why "the hotel" was requesting a wire transfer via WhatsApp.
The financial damage is real. UK fraud authorities logged 532 reports of Booking.com-related scams between June 2023 and September 2024... £370,000 in losses. Australian customers lost over $31 million in 2025 alone. And those are just the ones that got reported. Booking.com says financial data wasn't accessed from their systems, but that's a carefully worded statement. They don't need your credit card number if they have your reservation details. When a guest gets a message that says "Hi [Name], your booking at [Hotel Name] for [exact dates] requires a payment update," with every detail correct... most people comply. The contextual data IS the weapon. The booking details ARE the financial exploit, just with an extra step.
Look, the hospitality sector saw a 30% year-over-year increase in cyberattacks just in March 2026. This isn't a Booking.com problem. This is a structural vulnerability in how hotels operate. You've got high turnover staff (73% annually in hospitality), you've got shared workstations, you've got extranet credentials that probably haven't been rotated since the last GM left, and you've got a night shift with one person in the building who may or may not know what a phishing email looks like. The attack surface isn't the technology. It's the operational reality. Every vendor platform your property connects to... Booking.com, Expedia, your PMS, your payment processor... is only as secure as the person clicking links on that shared front desk computer at midnight.
Here's the Dale Test question (and if you've been reading my stuff, you know what that means): when that phishing email arrives at 2 AM, and it looks legitimate, and it asks your night auditor to click a link to "resolve a booking discrepancy"... what happens? If the answer is "they'd probably click it," you don't have a cybersecurity strategy. You have a countdown timer. The fix isn't a $50K security platform. It's a 30-minute training session, repeated quarterly, with specific examples of what these phishing attempts look like. It's two-factor authentication on every extranet login (Booking.com supports it... most properties don't enable it). It's a policy that says nobody on the overnight shift clicks any link from any OTA without calling a manager first. Simple. Unglamorous. Effective. The kind of thing that doesn't make it into a vendor's slide deck because you can't charge $3,000 a month for common sense.
Here's what to do this week. First, enable two-factor authentication on every OTA extranet account at your property... Booking.com, Expedia, all of them. Do it Monday. It takes ten minutes. Second, change every extranet password. If the same credentials have been active for more than 90 days, assume they're compromised. Third, run a 30-minute phishing awareness session with your front desk and reservations team. Show them actual screenshots of these "ClickFix" scam emails (they're all over cybersecurity blogs right now). Fourth... and this is the one people forget... brief your guest-facing staff on what to say when a guest calls asking about a suspicious payment request "from your hotel." Because those calls are coming. Your staff needs a script, not a deer-in-headlights moment. This is what I call the Invisible P&L... the costs that never show up on your financial statements but can destroy guest trust faster than a bad TripAdvisor review. A single scammed guest who blames your property is a reputation hit no marketing budget can fix. Get ahead of it.