Booking.com Got Breached. Your Front Desk Is About to Deal With the Fallout.
Hackers didn't steal credit cards from Booking.com... they stole something more useful: real guest names, real reservation details, and real property information. Now your guests are getting scam messages that look exactly like legitimate booking confirmations, and your front desk team is the last line of defense.
So here's what actually happened. Booking.com confirmed unauthorized access to customer booking data around April 13. Names, emails, phone numbers, addresses, specific reservation details... dates, property names, locations. Everything a scammer needs to craft a message so convincing that even a savvy traveler would hesitate before dismissing it. Booking says no financial data was compromised from their systems. That's technically accurate and practically irrelevant, because the scammers don't need your credit card number from Booking. They just need enough real information to trick you into handing it over yourself.
This is what the security world calls a "reservation hijack," and it's not new. The UK's Action Fraud documented 532 of these between June 2023 and September 2024, totaling roughly £370,000 in losses. What IS new is the scale and sophistication. The attackers are getting in through hotel partner accounts... phishing the properties themselves, compromising their Booking.com extranet credentials, and then using the platform's own messaging system to contact guests with legitimate-looking payment requests. AI is making these messages better, faster, more personalized. A guest gets a message through Booking's actual app referencing their actual reservation at your actual hotel asking them to "verify" payment. Most people would click. I might click. And that's the problem.
Look, I've evaluated dozens of vendor security architectures over the years. The pattern here is one I've seen over and over again: the platform secures its own perimeter, declares victory, and leaves the weakest node in the chain... the property... completely exposed. Booking invested heavily in AI fraud detection on their side. Great. But the attack vector isn't Booking's infrastructure. It's the hotel's. It's the GM who uses the same password for the extranet and their personal email. It's the front desk agent who clicks a phishing link at 2 AM because it looked like it came from Booking support. It's the property that has no two-factor authentication on their OTA accounts because nobody ever set it up and nobody ever asked. The platform treats security as its problem to solve centrally. But the breach happens locally, at the property, on the shift with the least technical person in the building.
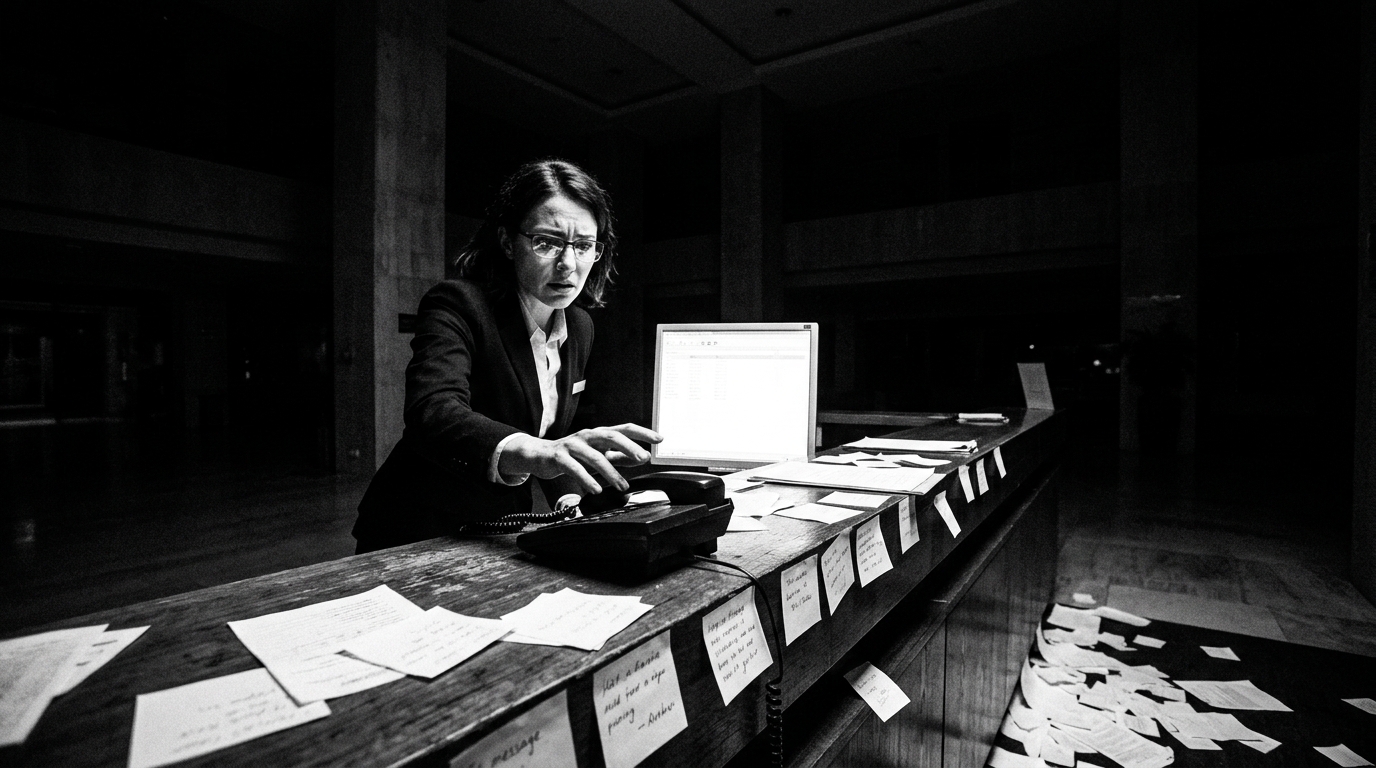
And here's what's going to hit operators hardest... it's not the breach itself. It's the phone calls. Guests who got scam messages are going to call your front desk. They're going to be angry, scared, confused. Your team needs to know what happened, what to say, and what NOT to say (do not confirm or deny specific reservation details over the phone to someone you can't verify... that's how the second wave of social engineering works). This is a training problem that landed on your doorstep this week whether you were ready for it or not. Booking reset reservation PINs for affected bookings. That's their fix. Your fix is making sure every person who answers your phone or stands behind your desk knows what a reservation hijack looks like and how to handle a guest who just got hit by one.
One more thing. Booking got fined €475,000 back in 2018 for reporting a breach 22 days late. They've been through this before. The question nobody's asking is whether the hotel partners whose accounts were compromised have any notification obligations of their own... and whether those partners even know their accounts were used as the entry point. If you're a property using Booking's extranet, check your account activity. Today. Not next week. Today. Because the attackers didn't break into Booking's vault. They walked in through your front door.
Here's what to do this week. First... every OTA extranet account at your property gets two-factor authentication turned on by Friday. Every. Single. One. If you don't know how, call your Booking rep and make them walk you through it. Second... brief your front desk team, especially your night shift, on what reservation hijack scams look like and how to handle guest calls about suspicious messages. The script is simple: "We will never ask for payment information by text or messaging app. If you received a message like that, do not click any links and contact us directly at this number." Third... check your Booking extranet login history right now. If you see logins from locations or devices you don't recognize, change credentials immediately and report it. This isn't about Booking's security problem. It's about yours. The platform got breached, but your property is the one taking the guest calls and absorbing the trust damage. Get ahead of it before your first angry guest walks up to the desk with a screenshot of a scam message that has your hotel's name on it.